Security researchers at Citizen Lab revealed the true spread of infamous mobile spyware ‘Pegasus’ as samples have been found in 45 countries all over the world – Over just the last two years. The spyware, which targets iPhones and Android devices, is developed by NSO Group, an Israeli company known for creating high-tech surveillance tools for intelligence agencies worldwide. Once a victim is infected the agency gains nearly complete access to their device including call and chat history, camera and microphone access, among others.
‘Pegasus’ spyware found in 45 countries
In a report published this Tuesday, the Citizen Lab at University of Toronto’s Munk School, an intedisciplinary laboratory, published a report containing a new approach to tracking the infamous mobile spyware Pegasus. Through extensive scanning the researchers at Citizen Lab identified over a thousand IP addresses matching the fingerprint of the spyware. Thereafter, by clustering the addresses into separate operators, 45 countries were exposed as locations where government agencies may have been conducting surveillance operations during the last two years.
Pegasus is made by NSO Group, an Israeli cyber intelligence firm known for selling high-tech surveillance tools. Similarly, services are also provided which include remotely cracking locked iPhones and Androids, all for intelligence agencies worldwide. The Pegasus tool can operate on both iPhone and Android devices and allows an attacker access to a very large amount of data: Text messages, chat history, emails, user location, microphone and camera access and so on.
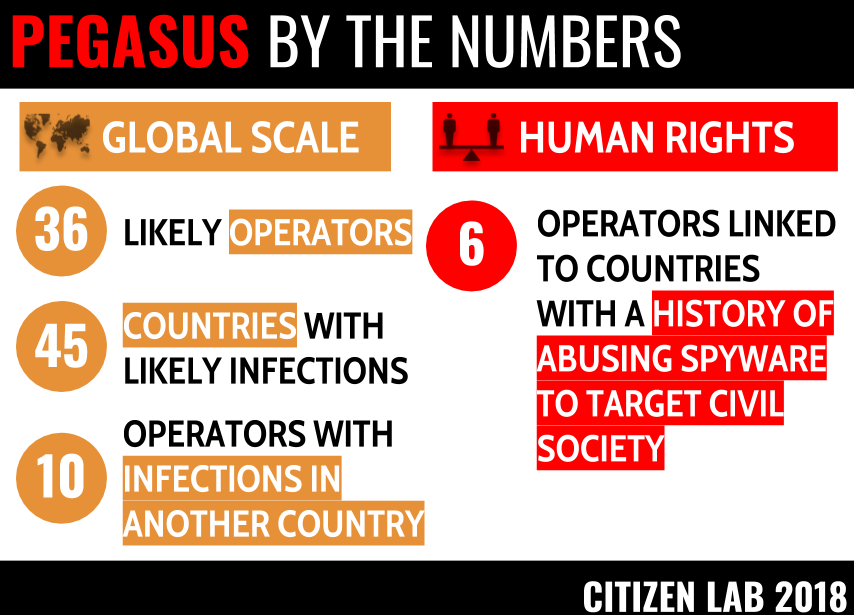
The spyware has given NSO group trouble in the past after Pegasus was found to have targeted human rights activists in countries like the United Arab Emirates. Within the report NSO Group are criticised for allowing oppressive regimes access to their spyware. However, democratic countries are not exempt from the list with Canada, France, the UK and USA being exposed. The full list of countries where instances of Pegasus were found on victim’s devices can be found in the official report.
NSO Group responds
Shalev Hulio, spokesperson for NSO Group released a statement in response to the report, highlighting that no laws had been broken by the company.
“Contrary to statements made by you, our product is licensed to government and law enforcement agencies for the sole purpose of investigating and preventing crime and terror. Our business is conducted in strict compliance with applicable export control laws”, reads his statement.
“NSO’s Business Ethics Committee, which includes outside experts from various disciplines, including law and foreign relations, reviews and approves each transaction and is authorized to reject agreements or cancel existing agreements where there is a case of improper use”.
The company also denied doing business in many of the countries listed in the report.

